Exoprise CloudReady synthetic sensors now support testing of Multi-factor Authentication (MFA). This enables you to use accounts that require MFA when it’s a tenant-wide setting, or provides the capability to test the reliability of MFA infrastructure.
Multi-factor Authentication has been known to cause frustration and even outages when it comes to Azure AD, Entra ID and Microsoft 365 Services:
MFA Outages
On September 28th, 2021, Microsoft suffered a global outage that prevented customers from logging into their Microsoft 365 accounts. According to the Microsoft Tech support team, the investigation pointed out the root cause of an issue with Multi-Factor Authentication. Read more about it here: https://www.exoprise.com/2022/02/01/multi-factor-authentication-synthetic-testing/
Background
Multi-factor Authentication (MFA) helps secure logins by requiring an additional authentication “factor” (source of verifiable secrets). The original factor is “something you know”, the password. The additional factor is “something you have”, a dedicated key fob or more typically now a cell phone running an authenticator app or receiving SMS.
For more information, take a look at the Microsoft page for MFA: https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-mfa-howitworks
For its security benefits, it’s not uncommon for MFA to be required tenant wide. MFA can also be a point of failure. There have been numerous Microsoft 365 outages related to MFA this past year, so it’s worth monitoring MFA and being informed of MFA related login problems.
Exoprise Implementation Overview
Exoprise supports testing MFA through Time-based One-Time Password (TOTP). TOTP is implemented by authenticator apps like “Microsoft Authenticator”, “Google Authenticator”.
- The server generates a TOTP secret key and shows it to the user as a QR code and a character string
- The user imports the TOTP_KEY into an authenticator app
- The authenticator uses the TOTP_KEY and the current time to generate a unique and ever changing one-time pass code (TOTP_CODE)
- Which is supplied to and verified by the server during login
- Because the server and the authenticator both have the TOTP_KEY, they will generate the same TOTP_CODE at a given time, which confirms the user’s ownership of the device with the TOTP_KEY
In order for Exoprise sensors to perform a TOTP-based login, they have to function like authenticator apps, i.e., have access to the TOTP_KEY to be able to generate TOTP_CODEs. The TOTP_KEY is supplied to the sensor during configuration and, like passwords, is securely stored with Public/Private Key (PKI) encryption. For more information about our Exoprise private site PKI, see the security overview.
At sensor runtime, the TOTP_KEY is utilized to generate the TOTP_CODE and submit it to the login MFA form. The sensor will try to detect and report any MFA related errors if TOTP_CODE submission fails.
How To Set up MFA For Synthetic Sensors
Obtaining the Time-based One-time Password (TOTP) Key
If the account you are using is not yet registered for MFA or is, but you want/need to generate a separate TOTP_KEY for the Exoprise sensors, you’ll need to follow the steps in this section.
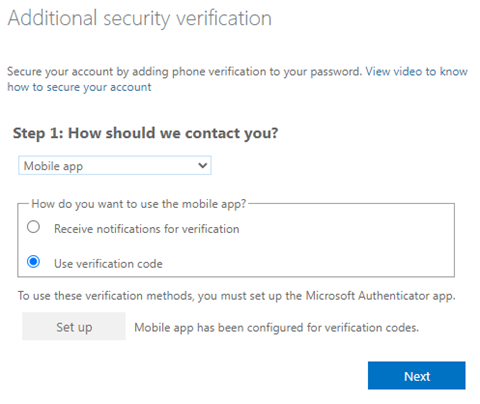
- If MFA is required but not yet set up, you will be redirected to https://account.activedirectory.windowsazure.com/proofup.aspx during login. If MFA is already set up, but you need/want to generate a new TOTP_KEY, you can open that page directly.
- Select Add Sign-in Method
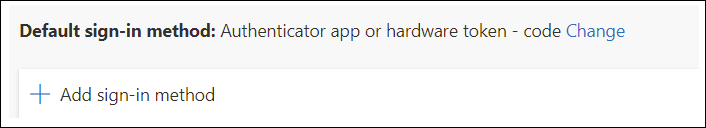
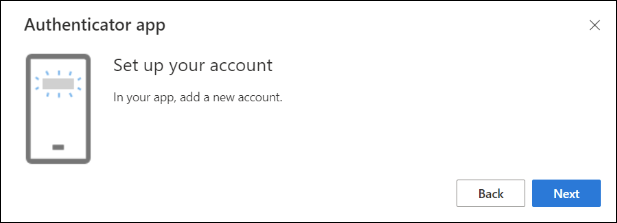
- Select Authenticator App and click Next
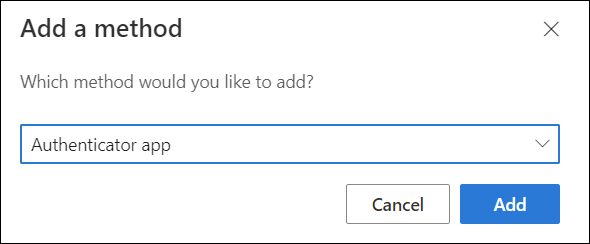
- Select I want to use a different authenticator app
- Click Next
- You’ll be presented with a QR Code and the “Can’t scan image?” option. Click on “Can’t scan image?” to generate the Secret Key
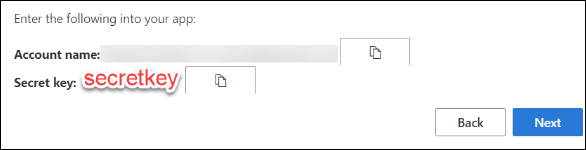
- Save the secret key. You will need to supply it in the sensor setup wizard. If you intend to set up other MFA-based synthetic testing sensors, you should save off the secret key, or you will need to re-register the MFA authentication later.
- To complete the registration, you’ll need to scan the QR code with or enter the “Secret Key” into an existing authenticator app (e.g. Microsoft Authenticator, Google Authenticator, Authy) after which the authenticator will start generating TOTP_CODEs.
- Click “Next” to close the popup and “Next” again in the main window
Verify the MFA Setup with Authenticator APP - To commit the MFA registration, enter the TOTP_CODE from the authenticator app
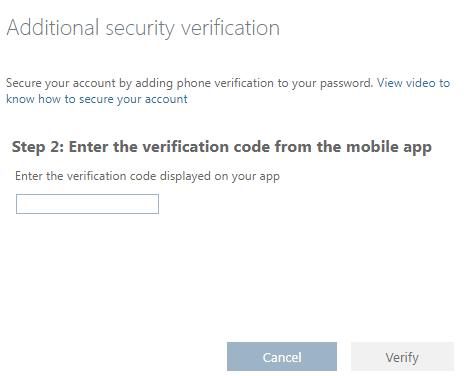
Commit the registration by entering a generated code - Microsoft may ask for a phone number in case you lose the authenticator.
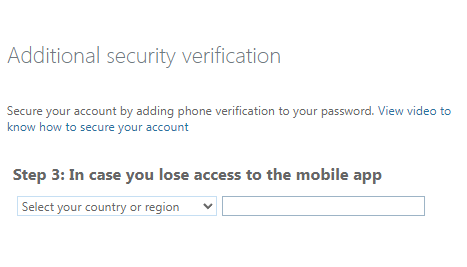
Additional prompt for a telephone number - If you have already set this up and want to generate a new TOTP_KEY for the sensors, the proofup.aspx page will look like this:
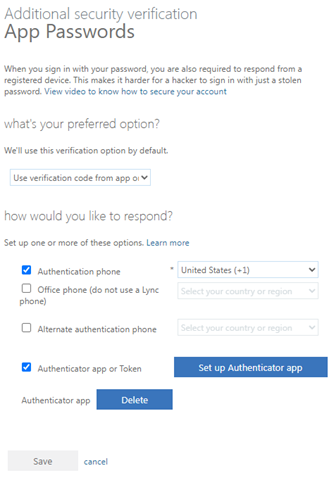
Generating Additional Secrete Keys
Supplying the TOTP_KEY to The Sensor
- For sensors that support Microsoft TOTP MFA, The sensor config wizard step where you enter credentials will have an optional “MFA TOTP Key” field in addition to the password field. See the following screenshot for an example of testing MFA with Microsoft Teams.
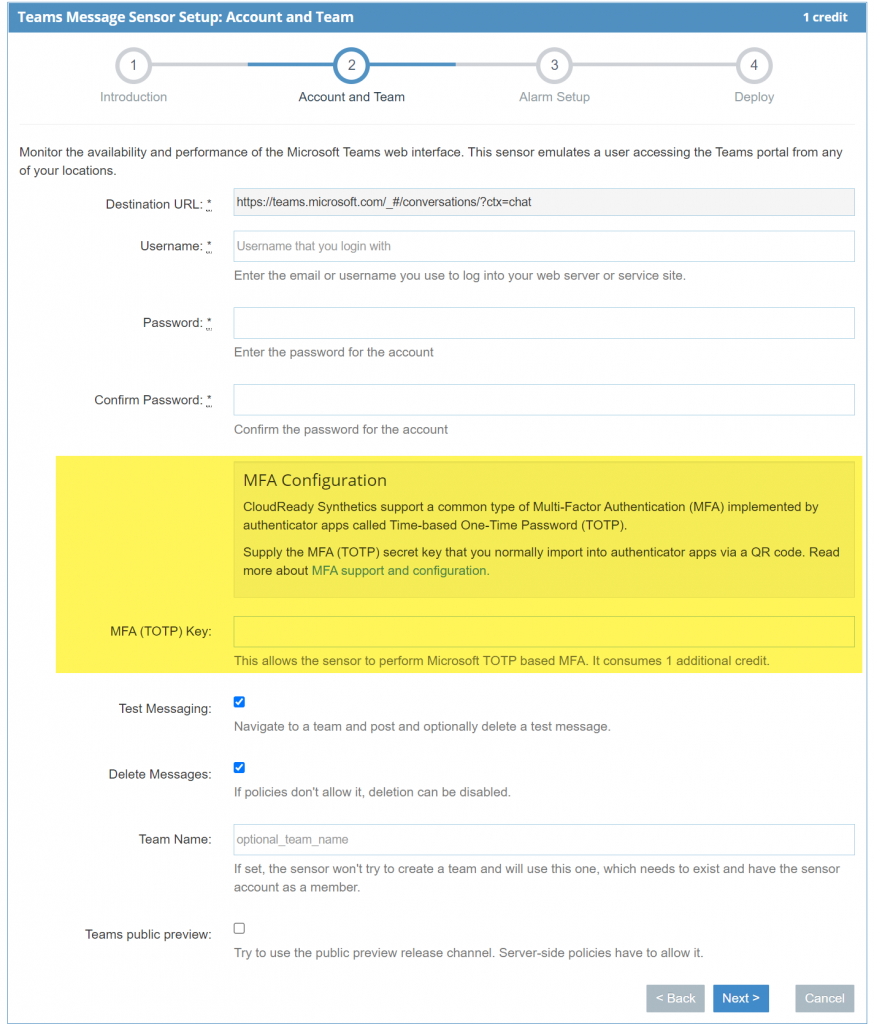
Exoprise CloudReady Synthetic Microsoft Teams MFA Setup - Enter the MFA TOTP Key into the provided field. A synthetic sensor that tests MFA will cost an additional Exoprise credit once deployed.
- When re-configuring the sensor, the TOTP Key won’t need to be re-entered unless you want to modify it, in which case you should uncheck the “keep existing” option.
Sensor-Specific Considerations for MFA Testing
Outlook Web Access or OWA
The OWA sensor has two aspects, mailbox access via the EWS API and browser-based mailbox testing via the Outlook Web Access interface for sending of test messages. The EWS API requests can be secured by basic auth (username/password) or OAuth. Basic auth has been deprecated and will be removed soon.
Microsoft 365 has two levels of MFA enforcement, enabled and enforced. When enabled, non-web-interactive (EWS API) authentication with the main account credentials continues to work, but when enforced, such authentication is blocked. So enforced MFA may result in OWA sensors errors like this:
Since Basic auth is deprecated, our recommendation to work around this is to switch to OAuth.